Announcing API abuse detection powered by machine learning
API security incidents are increasingly common and disruptive. With the growth of API traffic, enterprises across the world are also experiencing an uptick in malicious API attacks, making API security a heightened priority. According to our latest API Security Research Report, 50% of organizations surveyed have experienced an API security incident in the past 12 months and of those, 77% delayed the rollout of a new service or application.
At the RSA Conference 2023 today, we’re making it faster and easier to help detect API abuse incidents with the introduction of Advanced API Security Machine Learning powered abuse-detection dashboards. Our newly introduced Machine Learning models are trained to detect business logic attacks.
These types of attacks are notoriously hard to identify, and target APIs tied to intellectual property, business processes, or sensitive information, such as user data, listing of goods, or crediting accounts. These APIs must be accessible to provide business value, but have also become targets for attackers.
API security incidents can have a considerable impact on an organization’s operations and its bottom line. In June 2022, Imperva released a report titled Quantifying the Cost of API Insecurity, which estimates that lack of secure APIs could result in an average annual API-related total global cyber loss of between $41 billion to $75 billion annually. Furthermore, according to IBM’s 2022 Cost of a Data Breach Report, the average cost of a data breach is $4.35 million. It’s vital that organizations detect and mitigate API abuse incidents early to prevent prolonged fiscal and reputational damage to the business.
However, business logic attacks are harder to detect using static security policies, which allows attackers to manipulate legitimate functionality to achieve a malicious goal without triggering any static security alerts. For example, if a malicious actor gains control of a server and makes subtle changes, the shift in activity patterns of the server is generally undetectable to most monitoring tools. However, in this scenario, the Advanced API Security’s ML-powered API abuse detection model can help differentiate between legitimate and deviant traffic and immediately notify key stakeholders to act quickly and minimize blast radius of the problem.
The ML models that power API abuse detection have been trained and used by Google’s internal teams to help protect our public-facing APIs. The models rely on years of learning and best practices and are now available to all Apigee Advanced API Security customers.
Another challenge in detecting API abuse incidents is the volume of alerts. To reduce the risk of missing key security incidents, many static rules that detect less sophisticated attacks are incredibly sensitive: They generate a high volume of alerts. This makes finding the critical incidents within API traffic and acting to resolve them like “finding a needle in a haystack” for many IT teams. Apigee Advanced Security’s ML-powered dashboards more accurately identify critical API abuses and find similar patterns within the large number of bot alerts to help reduce the time to find and act on most important incidents.
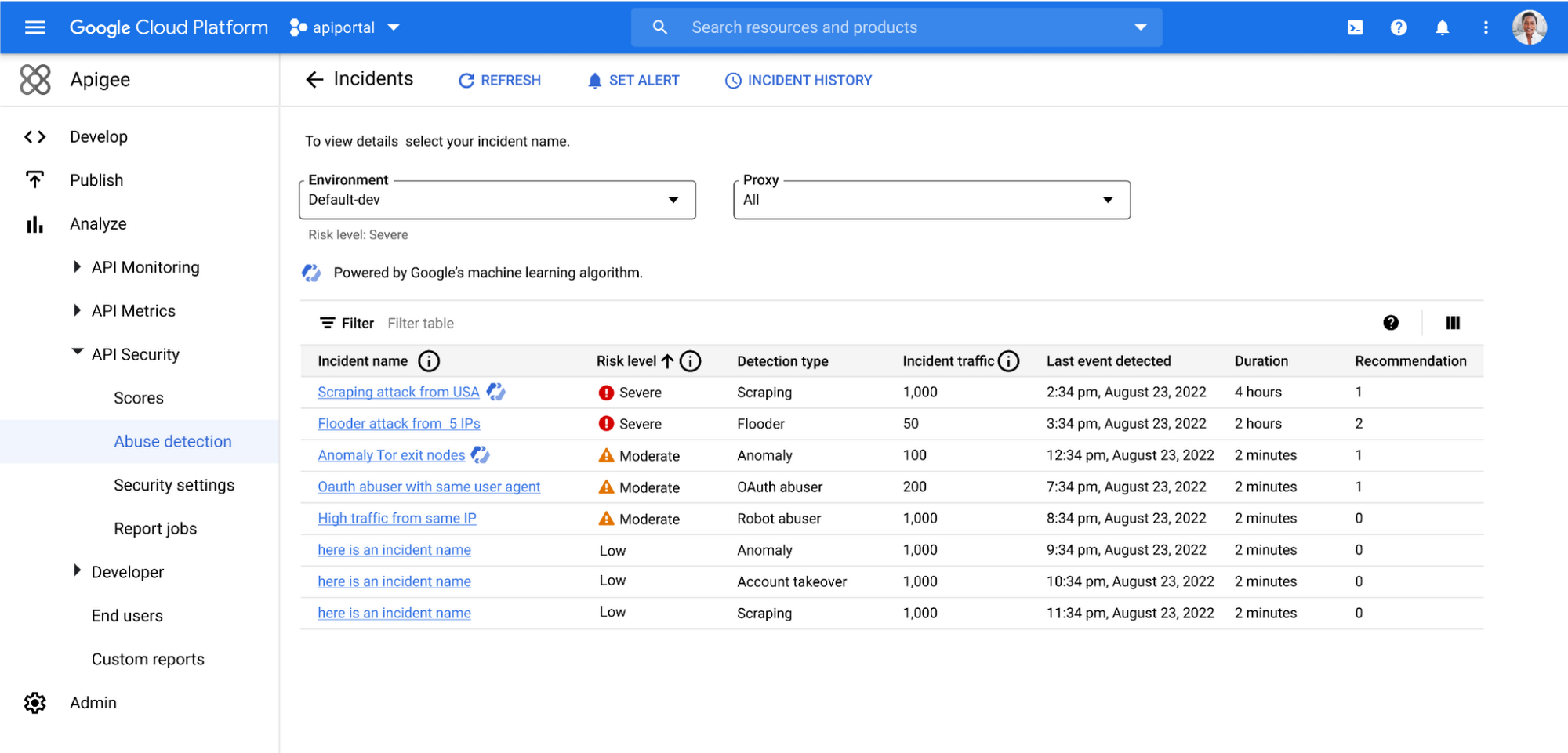
With the help of Apigee Advanced API Security’s ML-powered abuse detection dashboards, customers can uncover critical API abuse incidents, including business logic attacks, scraping, and anomalies, faster. Critical threats are surfaced with clear and concise descriptions to capture the essence of the attack along with the most important characteristics such as the source of the attack, the number of API calls, and the duration of the attack, to help resolve the incident more rapidly.

Machine Learning powered abuse-detection dashboards are available in Advanced API Security, a feature of Apigee API management that enables you to more easily detect API security misconfigurations, bad bots, and malicious activities.
